Guest Blogged by John Washburn
Currently, the public portions of the top to bottom review published by California last week have rightly been the subject of banner headlines. A report from the University of Connecticut, however, which was entitled "Integrity Vulnerabilities in the Diebold TSx Voting Terminal" and released a few days prior with not quite as much fanfare, provides an excellent counter to the oft-repeated vendor talking point that the California testing is similar to "giving keys to a thief."
The University of Connecticut report is immune to this specious argument. The University of Connecticut team had no access to source code or any information which was not publicly available. These limitations are precisely what all three vendors defined as "realistic" in their testimony in California at the public hearing on Monday July, 30, 2007. Yet, under these vendor-approved conditions, the University of Connecticut found yet another set of new, serious, and election altering defects and was able to exploit them in a disturbingly effective manner.
The primary finding of the report is that in a "sleepover" situation where the TSx DRE is sent home with the poll worker days or in the case of San Diego weeks ahead of time, it is possible to alter the ballot definitions of the DRE. The alteration would create the behavior where the votes for two candidates are exchanged. Thus, the voter touches the screen next to name of John Smith, the screen lights up the selection for John Smith, the voter verifiable paper audit trail prints the name John Smith, but, nonetheless, the invisible electronic ballot accrues the vote to Pocahontas. Similarly, voters intending to vote for Pocahontas would have their votes accrue to John Smith. This is a straight up exchange of votes between two candidates.
The report also mentions how to suppress the display of a given candidate.
This exploit manipulates the ballot definition and nothing else. The successful exploits in the UCONN report take advantage of the fact that the ballot definition is split between the election database and the display portion stored the .XTR files, but without corresponding mechanisms to maintain referential integrity between the two halves of the ballot definition. The election database portion of the ballot definition controls how votes accrue to candidates based on the ballot line. The display portion of the ballot definition controls how names are printed on the screen and VVPAT record based on the ballot line. Both exploits introduce a referential integrity break between these two halves of the ballot definition.
In the example above, the election database has Pocahontas and Smith on ballot lines 5 and 20; respectively. By swapping the .XTR files, the display portion of the ballot definition has Pocahontas on ballot line 20 and Smith on ballot lines 5. Thus, a screen touch to ballot line 5 accrues a vote to the candidate assigned to ballot line 5. According the election database portion of the ballot definition, this is Pocahontas. The screen and VVPAT print the name associated with ballot line 5. According the display portion of the ballot definition (the .XTR files) this is Smith. Thus, both the screen and VVPAT say Smith, but the vote on the invisible electronic ballot actually accrues to Pocahontas.
- IF a VVPAT trail exists and,
- IF the VVPAT trail is undamaged
and,
- IF an audit is actually performed, then, and only then,
-
would a careful audit of the VVPAT audit trail discover this manipulation of
the ballot definition.
The needed tools for either of these exploits are:
- 1) A laptop with a PCMCIA card reader,
- 2) One of the following three: a screw driver, lock picking skills, or a hotel mini-bar key, and
- 3) The desire to "take one for the team" and commit a felony to further your candidate.
It must be stressed again that this all was discovered with nothing more than access to the DRE machine. This examination was under vendor-approved conditions. There was no access to any information an election official would not normally have or any information which a determined citizen could not find out during a DRE sleepover prior to an election.
The take away here is that if you can poison the well, the computer programming and/or configuration files in the DRE, everything which proceeds from the DRE is potentially corrupted as well. The UCONN report demonstrates the Diebold TSx DRE can produce consistent election records that are not accurate election records.


 TEAM BLUE TRIUMPH! Dems Win Everything Everywhere All at Once: 'BradCast' 11/5/25
TEAM BLUE TRIUMPH! Dems Win Everything Everywhere All at Once: 'BradCast' 11/5/25 Repub Thuggery As Americans Vote: 'BradCast' 11/4/25
Repub Thuggery As Americans Vote: 'BradCast' 11/4/25 'Green News Report' 11/4/25
'Green News Report' 11/4/25
 Last Call(s) Before Election Day: 'BradCast' 11/3/25
Last Call(s) Before Election Day: 'BradCast' 11/3/25 Sunday 'Close Enough' Toons
Sunday 'Close Enough' Toons A Pretty Weak 'Strongman': 'BradCast' 10/30/25
A Pretty Weak 'Strongman': 'BradCast' 10/30/25 'Green News Report' 10/30/25
'Green News Report' 10/30/25 Proposal for 'First Politically Viable Wealth Tax' Takes Shape in CA: 'BradCast' 10/29
Proposal for 'First Politically Viable Wealth Tax' Takes Shape in CA: 'BradCast' 10/29 Monster Storm, Endless Wars, Gamed Elections: 'BradCast' 10/28/25
Monster Storm, Endless Wars, Gamed Elections: 'BradCast' 10/28/25 'Green News Report' 10/28/25
'Green News Report' 10/28/25 Let's Play 'Who Wants to Be a U.S. Citizen?'!: 'BradCast' 10/27/25
Let's Play 'Who Wants to Be a U.S. Citizen?'!: 'BradCast' 10/27/25 Sunday 'Cartoonists Dilemma' Toons
Sunday 'Cartoonists Dilemma' Toons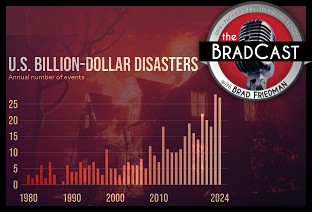 Exiled NOAA Scientists Resurrect Critical Disaster Database: 'BradCast' 10/23/25
Exiled NOAA Scientists Resurrect Critical Disaster Database: 'BradCast' 10/23/25 'Green News Report' 10/23/25
'Green News Report' 10/23/25 Trump-Allied GOP Partisan Buys Dominion Voting Systems: 'BradCast' 10/22/25
Trump-Allied GOP Partisan Buys Dominion Voting Systems: 'BradCast' 10/22/25 Trump, Republican Law(lessness) & (Dis)Order: 'BradCast' 10/21/25
Trump, Republican Law(lessness) & (Dis)Order: 'BradCast' 10/21/25 Celebrating 'No Kings': 'BradCast' 10/20/25
Celebrating 'No Kings': 'BradCast' 10/20/25 SCOTUS Repubs Appear Ready to Gut Rest of Voting Rights Act: 'BradCast' 10/16/25
SCOTUS Repubs Appear Ready to Gut Rest of Voting Rights Act: 'BradCast' 10/16/25 The 'Epstein Shutdown' and Other Autocratic Nightmares: 'BradCast' 10/15/25
The 'Epstein Shutdown' and Other Autocratic Nightmares: 'BradCast' 10/15/25 Group Vows to Block MO's GOP U.S. House Gerrymander: 'BradCast' 10/14/25
Group Vows to Block MO's GOP U.S. House Gerrymander: 'BradCast' 10/14/25 Trump Labor Dept. Warns Trump Policies Sparking Food Crisis: 'BradCast' 10/9/25
Trump Labor Dept. Warns Trump Policies Sparking Food Crisis: 'BradCast' 10/9/25 Trump's Losing Battles: 'BradCast' 10/8/25
Trump's Losing Battles: 'BradCast' 10/8/25
 VA GOP VOTER REG FRAUDSTER OFF HOOK
VA GOP VOTER REG FRAUDSTER OFF HOOK Criminal GOP Voter Registration Fraud Probe Expanding in VA
Criminal GOP Voter Registration Fraud Probe Expanding in VA DOJ PROBE SOUGHT AFTER VA ARREST
DOJ PROBE SOUGHT AFTER VA ARREST Arrest in VA: GOP Voter Reg Scandal Widens
Arrest in VA: GOP Voter Reg Scandal Widens ALL TOGETHER: ROVE, SPROUL, KOCHS, RNC
ALL TOGETHER: ROVE, SPROUL, KOCHS, RNC LATimes: RNC's 'Fired' Sproul Working for Repubs in 'as Many as 30 States'
LATimes: RNC's 'Fired' Sproul Working for Repubs in 'as Many as 30 States' 'Fired' Sproul Group 'Cloned', Still Working for Republicans in At Least 10 States
'Fired' Sproul Group 'Cloned', Still Working for Republicans in At Least 10 States FINALLY: FOX ON GOP REG FRAUD SCANDAL
FINALLY: FOX ON GOP REG FRAUD SCANDAL COLORADO FOLLOWS FLORIDA WITH GOP CRIMINAL INVESTIGATION
COLORADO FOLLOWS FLORIDA WITH GOP CRIMINAL INVESTIGATION CRIMINAL PROBE LAUNCHED INTO GOP VOTER REGISTRATION FRAUD SCANDAL IN FL
CRIMINAL PROBE LAUNCHED INTO GOP VOTER REGISTRATION FRAUD SCANDAL IN FL Brad Breaks PA Photo ID & GOP Registration Fraud Scandal News on Hartmann TV
Brad Breaks PA Photo ID & GOP Registration Fraud Scandal News on Hartmann TV  CAUGHT ON TAPE: COORDINATED NATIONWIDE GOP VOTER REG SCAM
CAUGHT ON TAPE: COORDINATED NATIONWIDE GOP VOTER REG SCAM CRIMINAL ELECTION FRAUD COMPLAINT FILED AGAINST GOP 'FRAUD' FIRM
CRIMINAL ELECTION FRAUD COMPLAINT FILED AGAINST GOP 'FRAUD' FIRM RICK SCOTT GETS ROLLED IN GOP REGISTRATION FRAUD SCANDAL
RICK SCOTT GETS ROLLED IN GOP REGISTRATION FRAUD SCANDAL VIDEO: Brad Breaks GOP Reg Fraud Scandal on Hartmann TV
VIDEO: Brad Breaks GOP Reg Fraud Scandal on Hartmann TV RNC FIRES NATIONAL VOTER REGISTRATION FIRM FOR FRAUD
RNC FIRES NATIONAL VOTER REGISTRATION FIRM FOR FRAUD EXCLUSIVE: Intvw w/ FL Official Who First Discovered GOP Reg Fraud
EXCLUSIVE: Intvw w/ FL Official Who First Discovered GOP Reg Fraud GOP REGISTRATION FRAUD FOUND IN FL
GOP REGISTRATION FRAUD FOUND IN FL

































